Overview
CyLock MFA enables strong Multi-Factor Authentication for any firewall based SSL VPN user login. CyLock MFA integrates with the firewall through CyLock MFA RADIUS proxy component installed in a server within the organization’s local network.
The CyLock MFA RADIUS proxy component enables any firewall with RADIUS protocol support to carry out a strong Multi-Factor Authentication (MFA) during remote login to remote network through SSL VPN.
Supported Devices:
Firewall Devices: PA-200 series, PA-400 series, PA-800 series, PA-3200 series, PA-5000 series, PA-7000 series supports RADIUS authentication.
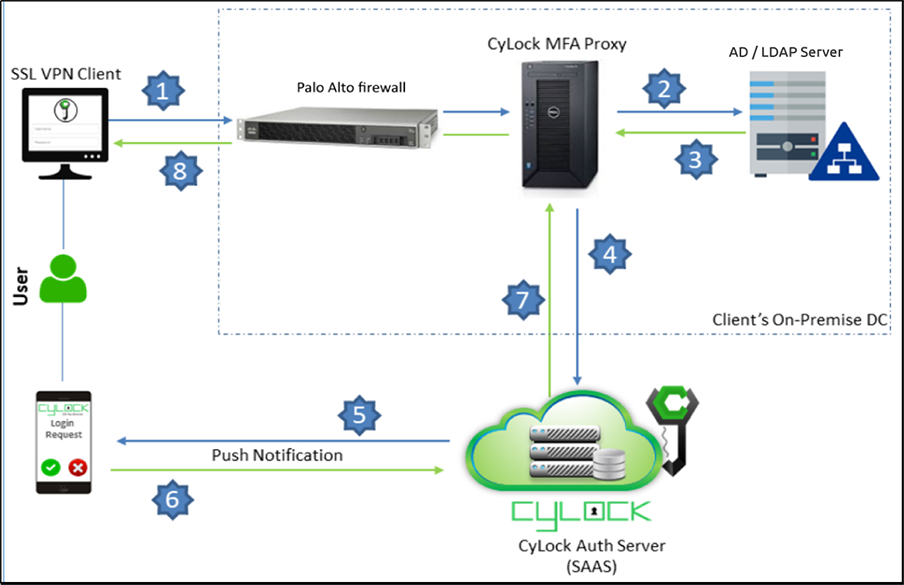
Architecture Overview
CyLock MFA RADIUS proxy component needs to be installed within your network to enable MFA during SSL VPN login process. First factor (user login credentials) can be authenticated with an on-premise AD / LDAP / LDAP Server or against CyLock MFA local store. A typical deployment architecture and process is shown below.
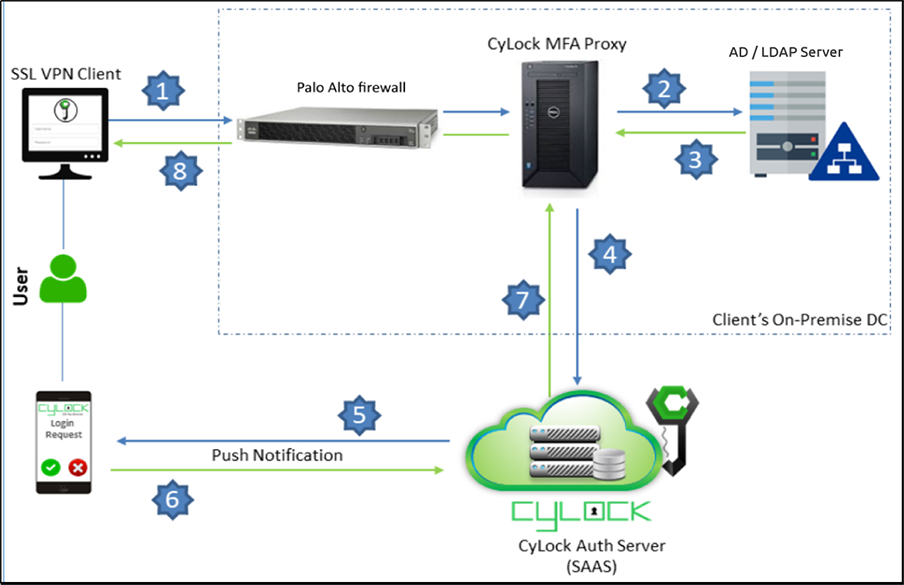
Figure 1 – Deployment Architecture Block diagram of integrating Fortinet Firewall with CyLock RADIUS Proxy
Note:
- CyLock MFA RADIUS Proxy communicates with CyLock MFA Auth Server on TCP port 443
- Any firewall configuration to restrict access to CyLock MFA Auth Server through destination IP address or IP address ranges is not recommended as the IP addresses may change to provide service high availability
Prerequisites
- Securing an application requires an active CyLock MFA account. (Refer “Getting Started: Guide to CyLock MFA” to start using CyLock MFA to protect your applications).
- Login to “CyLock MFA Portal”
- Navigate to Application menu in the left menu panel
- Click “Add Application” button to secure an application. Locate and select “SSL VPN” from the list of application names. Click “+Secure” button to configure CyLock MFA for SSL VPN. Enter the details as requested and click “Save” button. Before leaving the page copy Application Key and Application ID, which are required during CyLock MFA RADIUS Proxy component installation. See “Securing an Application” for more information about protecting applications in CyLock MFA.
- Node.JS to be installed in the server where the CyLock MFA RADIUS Proxy component will be deployed.
- Download the CyLock MFA RADIUS Proxy component from the URL
https://downloads.cybernexa.com/downloads/CyLock_radius_proxy.zip
.
- Follow the instructions in “CyLock MFA RADIUS Proxy Installation” section to enable Multi-Factor Authentication (MFA) for SSL VPN user login
- Verify Microsoft AD / LDAP is installed and configured for authenticating first factors of users
- Download CyLock MFA Mobile App from Play Store or iOS store
- Register SSL VPN user using CyLock MFA Mobile app.
CyLock MFA RADIUS Proxy Installation
CyLock MFA RADIUS Proxy component will receive incoming RADIUS requests from your firewall during SSL VPN login. The proxy component will then perform the primary authentication (first factor authentication) either with your internal AD / LDAP Server / LDAP Server or CyLock MFA local store, and then contact CyLock MFA Auth Server for second factor authentication.
CyLock MFA RADIUS Proxy can be installed on a physical or virtual host within your network. We recommend a system with at least 4 vCPU, 200 MB disk space, and 4 GB RAM. CyLock MFA RADIUS Proxy supports the following operating systems:
- Windows Server 2008 or later (Server 2016+ recommended)
- CentOS 7 or later (CentOS 8+ recommended)
- Red Hat Enterprise Linux 7 or later (RHEL 8+ recommended)
- Ubuntu 18.04 or later (Ubuntu 20.04+ recommended)
- Debian 7 or later (Debian 9+ recommended)
Install Node.JS in the server where the CyLock MFA RADIUS Proxy component will be installed.
Download the CyLock MFA RADIUS Proxy component. Refer Prerequisites section above. After downloading, copy/move the Proxy Component to the respective server.
Configuring CyLock MFA RADIUS Proxy component
Go to the folder where the Proxy component has been copied. Extract the CyLock_radius_proxy.zip. After extracting, follow the below steps to configure the component.
On Windows or Linux machine go to the respective folder where the proxy component was copied & extracted.
MFA Configuration:
Open the cyconfig.js file in CyRadius Folder with administrative privileges and change the following properties:
| # |
Property Name (key) |
Description (value) |
| 1 |
url |
Enter Auth URL (Ex - https://demoauth.cybernexa.com/api/v2/srv/)
Contact the CyLock Support Team to get the Auth Server URL.
|
| 2 |
id_sp |
Customer ID value. Refer point #4 in Prerequisites section. |
| 3 |
Authorization |
API Key value. Refer point #4 in Prerequisites section. |
| 4 |
radius_secret |
Paste the Encrypted Radius secret key. To obtain the encrypted RADIUS Secret key, please refer to the Key Encryption Process Section listed below.
|
Note: Do not modify the key in the key-value pair.
AD / LDAP Configuration:
To enable RADIUS Proxy component, communicate with MS AD / LDAP server or LDAP server, configure the adconfig.js file.
Open the adconfig.js file in CyRadius Folder with administrative privileges and change the below properties.
| # |
Property Name (key) |
Description (value) |
| 1 |
Open_ldap_server |
Enter your open ldap server URL (ex: ldaps://ldap.cybernexa.com)
|
| 2 |
domain |
Provide your AD / LDAP domain name. |
| 3 |
url |
For secured LDAP:
ldaps://computername.domain.com or else simply use
For normal LDAP:
ldap://computername.domain.com
|
| 4 |
baseDN |
AD / LDAP Domain name |
| 5 |
Password |
Paste Your AD / LDAP server Administrator user’s Encrypted password. To obtain the encrypted AD / LDAP Password, please refer to the Key Encryption Process Section listed below. |
Note: Do not modify the key in the key-value pair.
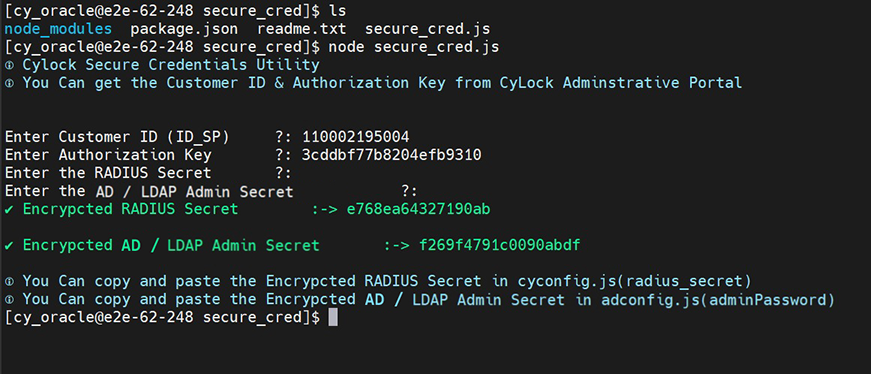
Key Encryption Process:
Encrypting Radius Secret Key and AD / LDAP Password.
a. After Unzip the radius_proxy.zip file. Go to the secure_cred directory and execute the "secure_cred.js" file using the command below
(i).node secure_cred.js
- Enter Customer ID (ID_SP): Get the ID_SP Key from the CyLock Portal. Refer Point #4 in Prerequisites Section.
- Enter Authorization Key: Get the API Key from the CyLock Portal. Refer Point #4 in Prerequisites Section.
- Enter Radius Secret: This Radius secret key is used to communicate between the firewall and the Radius Proxy server.
- Enter AD / LDAP Admin Secret: Enter Your AD / LDAP Admin Password Refer Figure 2.
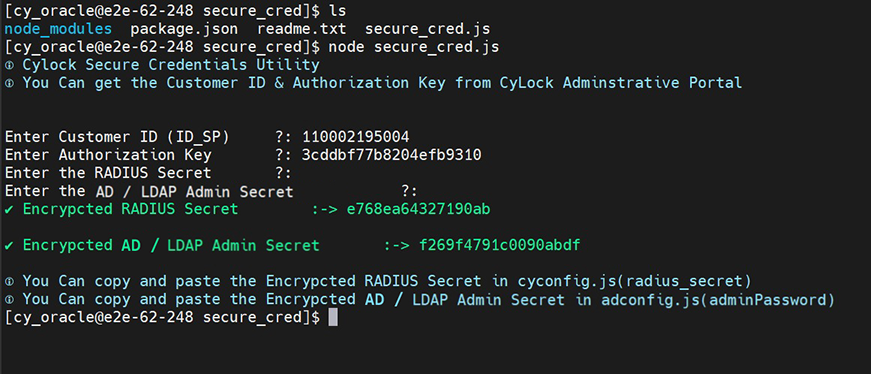
Figure 2 – Encrypting RADIUS Secret and AD / LDAP Password
Copy and paste the Encrypted RADIUS Secret into the “radius_secret” field in cyconfig.js file.
Copy and paste the Encrypted AD / LDAP Admin Secret into the “password" filed in adconfig.js file.
Note:The RADIUS Secret and AD / LDAP Password should always be encrypted.
Starting CyLock MFA RADIUS Proxy
Manual Start (Windows and Linux):
- Open terminal window
- Go to the folder where CyLock MFA RADIUS proxy component was copied
- Execute the command “node radius.js”
Auto Start (Linux):
To start the component automatically create and run as service
For creating service file follow the below steps:
- Open terminal window
- Execute
vi/etc/systemd/system/cylockradiusservice.service
- Copy and paste the below contents from start of the file to end of the file in cylock radius service file.
//*****Start of the file*****
[Unit]
Description=cylockradiusservice
After=syslog.target
After=network.target[Service]
User=cylock_iam
//Replace with your system user name
Type=simple
[Service]
Restart=always
StandardOutput=syslog
StandardError=syslog
//Provide the path of the CyLock MFA RADIUS proxy component (server.js)
WorkingDirectory=/home/cylock_iam/package/
//Provide the path of the CyLock MFA RADIUS proxy component (server.js)
ExecStart=/usr/bin/node /home/cylock_iam/package/server.js
SyslogIdentifier=cylockradiusservice
[Install]
1.WantedBy=multi-user.target
//******End of the file******
- 4.Save and exit vi editor by entering the following command
a.:wq!
- 5.Enable the service by entering the following command
a.systemctl enable cylockradiusservice.service
- 6.Start the service by entering the following command.
a.systemctl start cylockradiusservice.service
Note:For Windows OS, create a service for the batch file (.bat) using nssm.exe utility and start the service.
Configuring Firewall Settings
CyLock MFA integrates with your firewall device based VPN via RADIUS to add Multi-Factor Authentication (MFA) to SSL VPN login. In this context your firewall device will act as RADIUS client and the CyLock MFA RADIUS Proxy component as the RADIUS server.
Configuring the Palo Alto Firewall for RADIUS Authentication
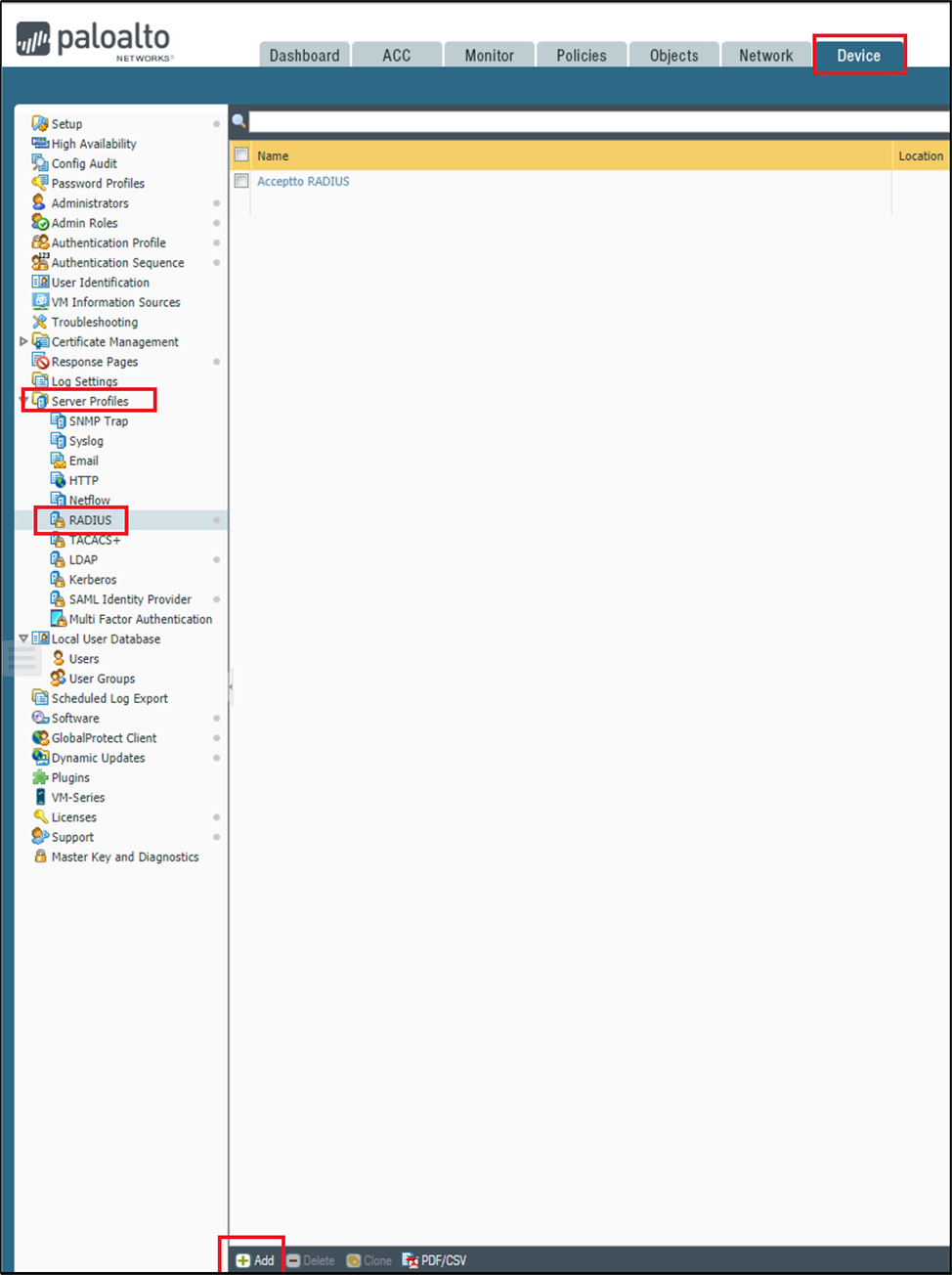
- Configure a RADIUS Server:
- Open the Palo Alto administrative interface and navigate to Device tab > Server
Profiles > RADIUS and click Add at bottom of the portal page.
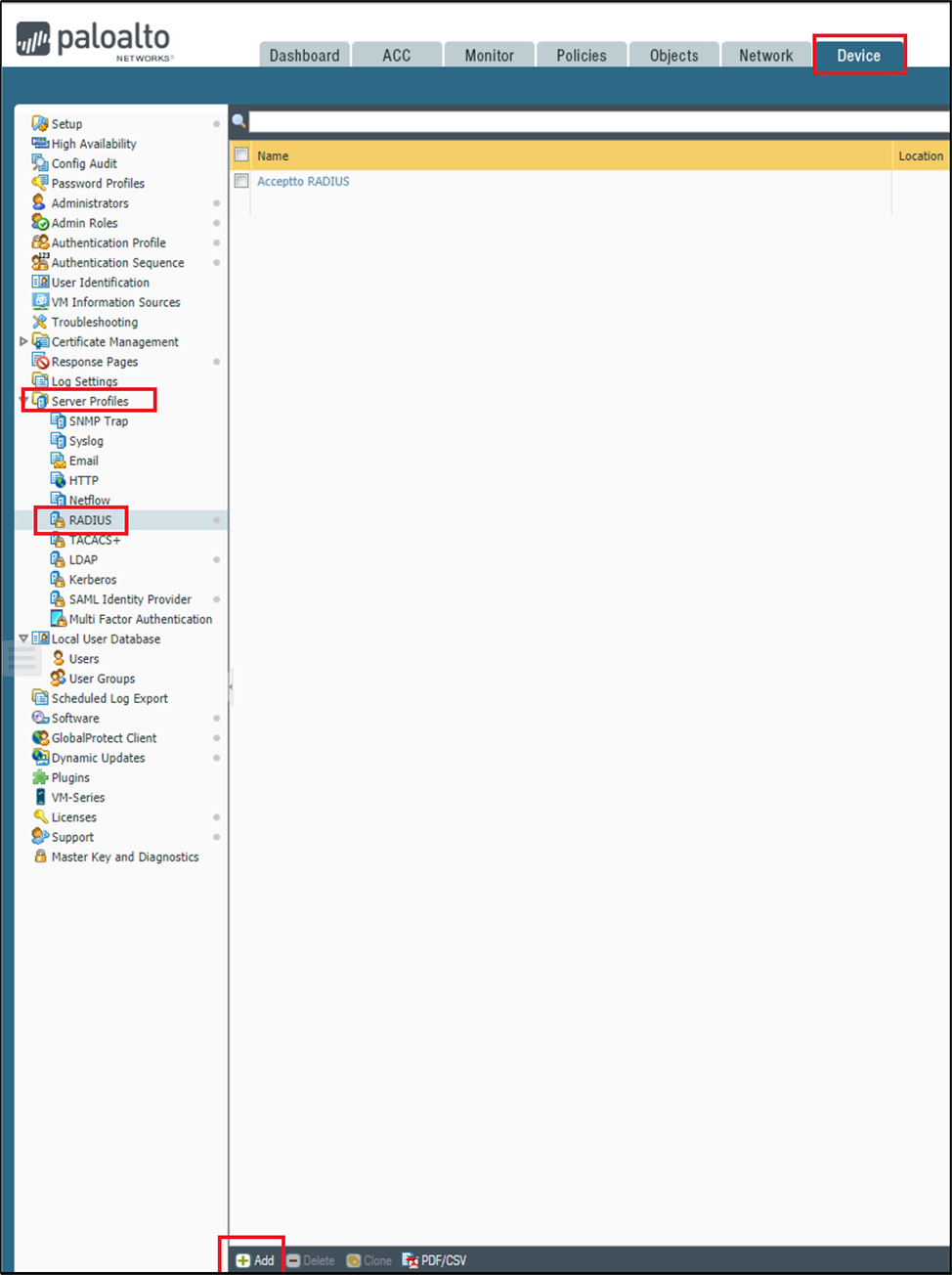
Figure 3 – Palo Alto Firewall Dashboard
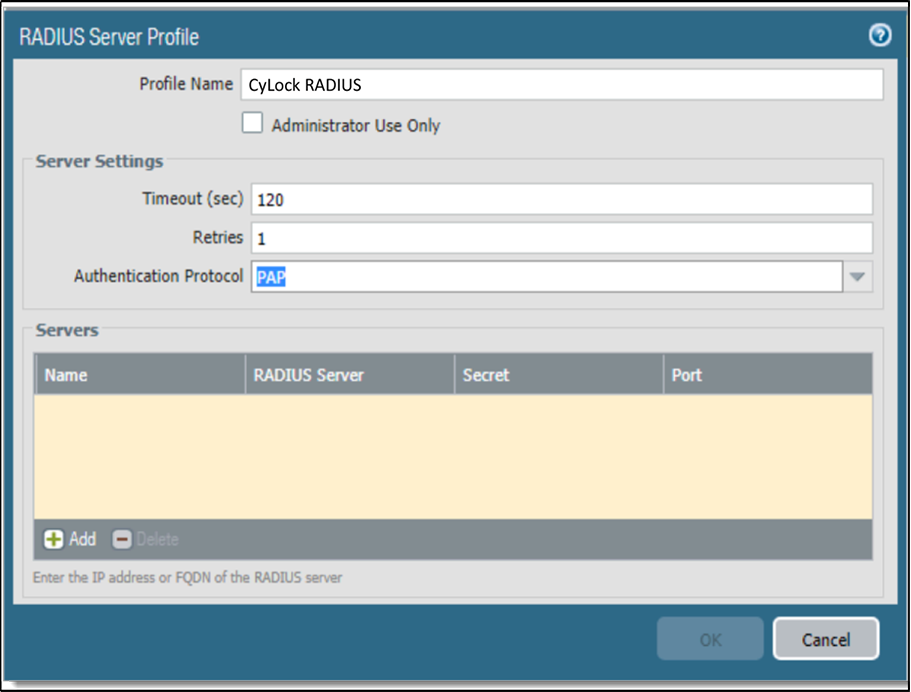
- In the RADIUS Server profile dialog, enter the configuration for your RADIUS
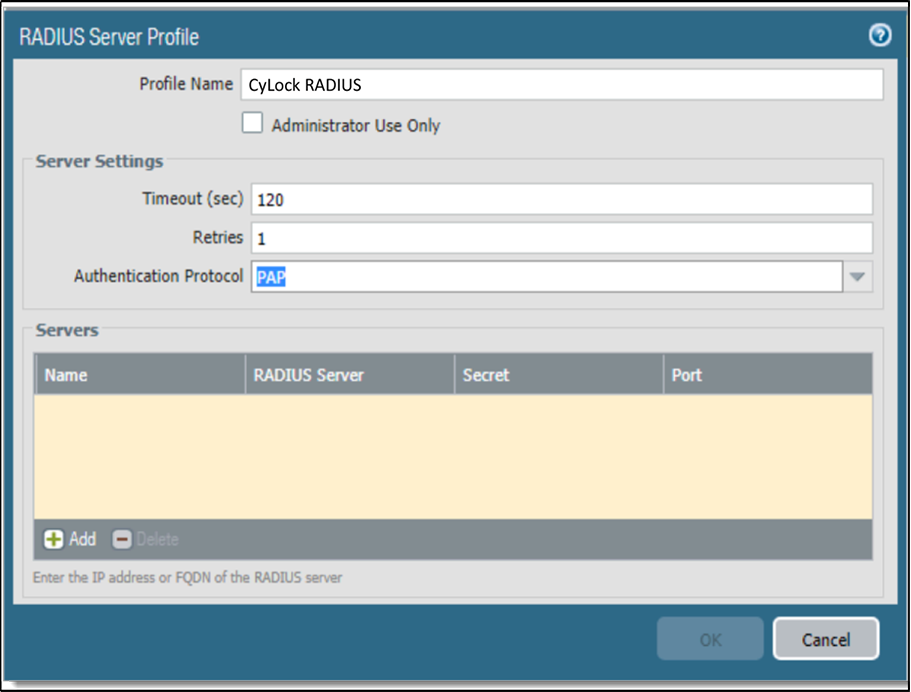
Figure 4 – Entering Radius Timeout and Protocol
Profile Name:Enter a friendly name for this configuration.
Timeout (sec):120 seconds
Retries:1
Authentication Protocol:PAP
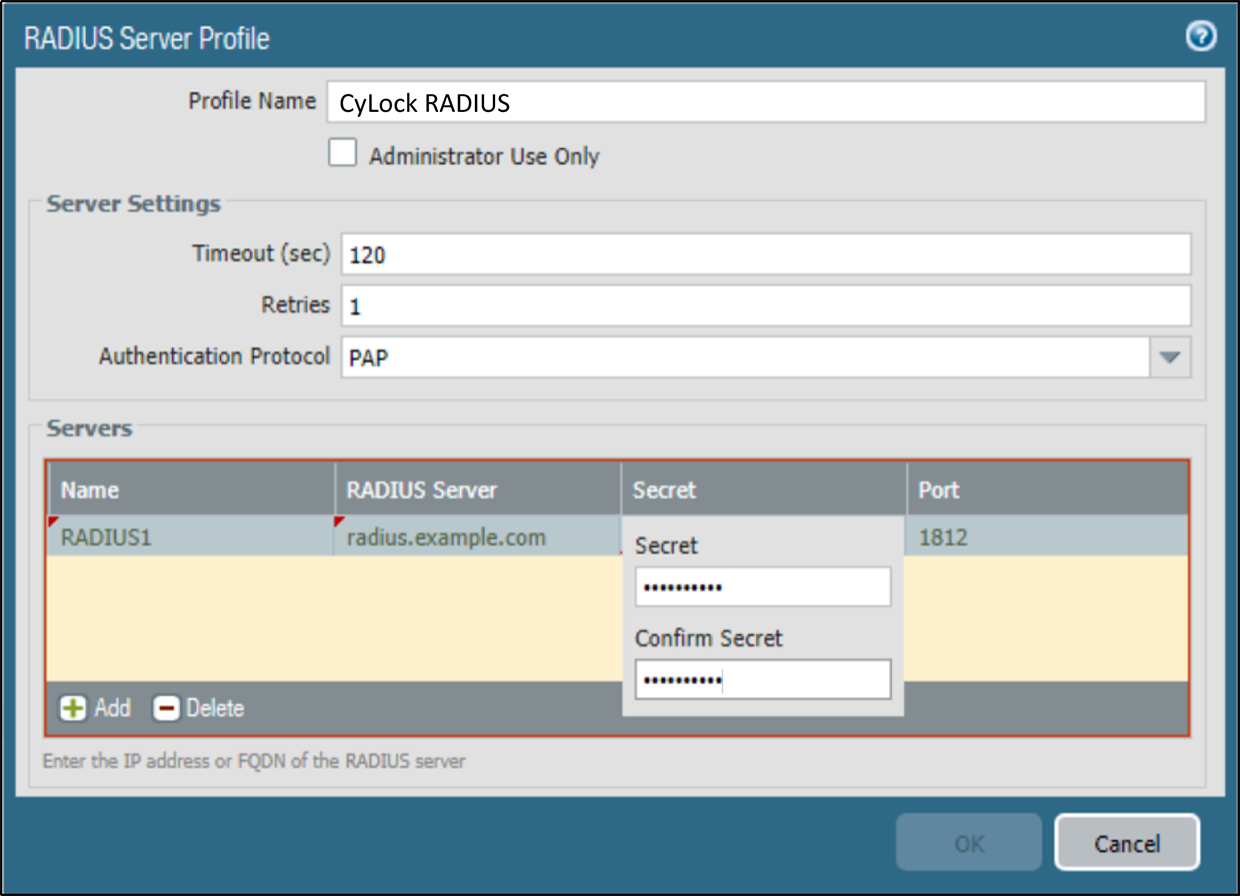
- Select the Add button at the bottom of the dialog to add a new RADIUS server.
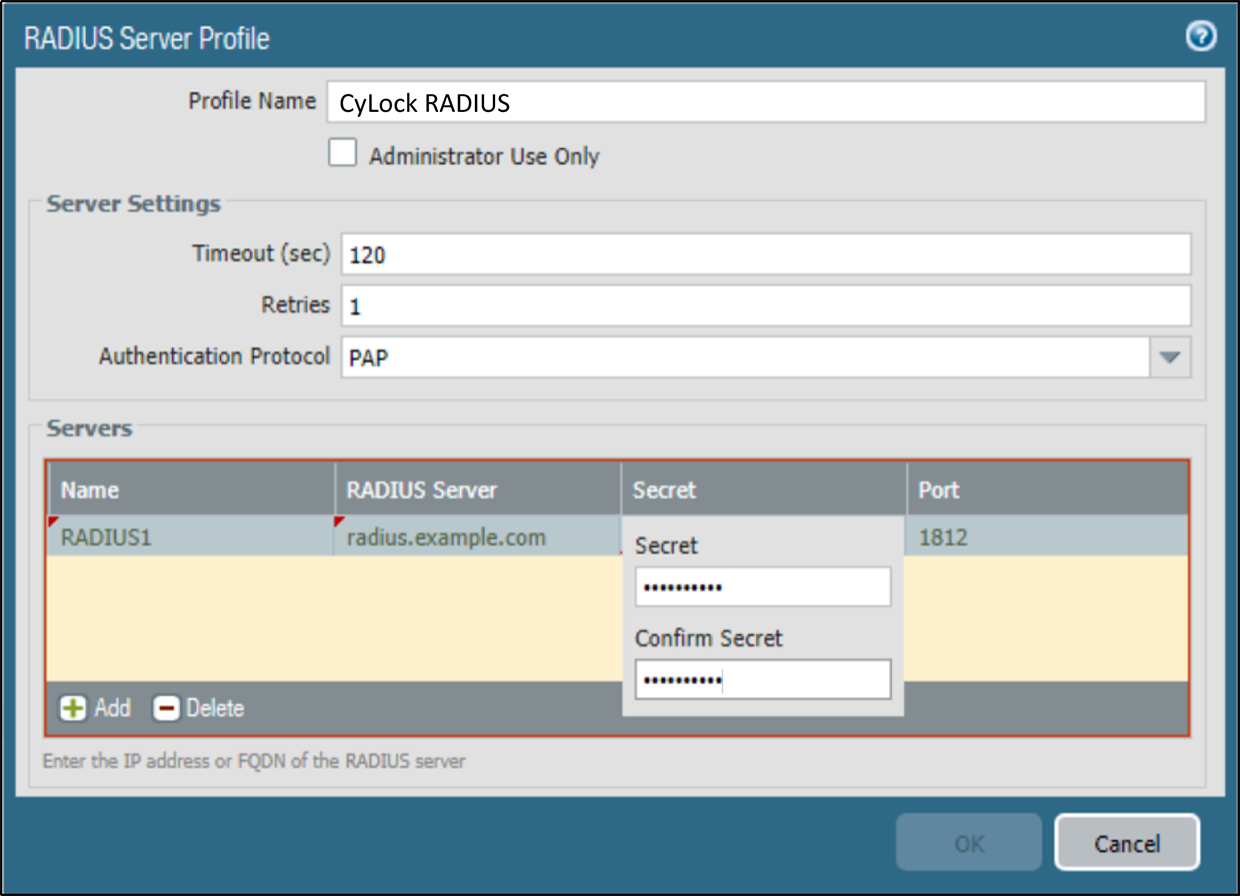
Figure 5 – Configuring Radius Server Details
Name:A friendly name for the RADIUS Server (ex: CyLock RADIUS)
RADIUS Server:The IP address or Fully Qualified Domain Name (FQDN) of your RADIUS server.
Secret::The string used to authenticate the Palo Alto Device to the RADIUS Server.
Port:Leave this unchanged.
- Select OK and then Commit.Your new RADIUS Server Profile is ready to use.
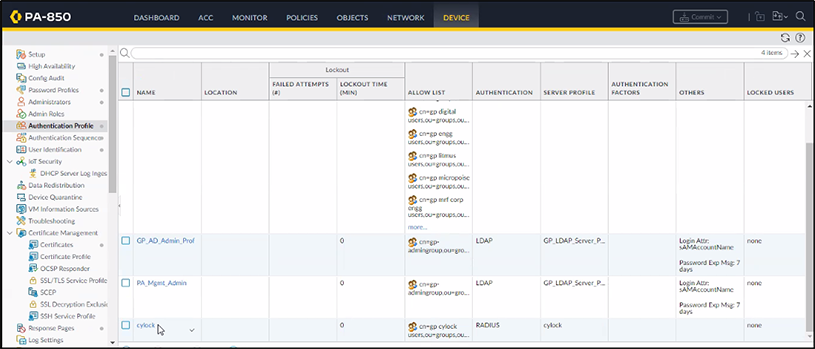
- Configure Authentication profile and Authentication Sequence.
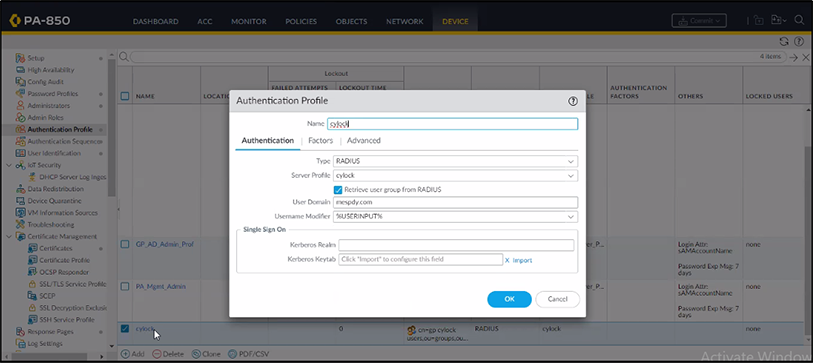
- Click Authentication Profile, then double-click the CyLock Profile.
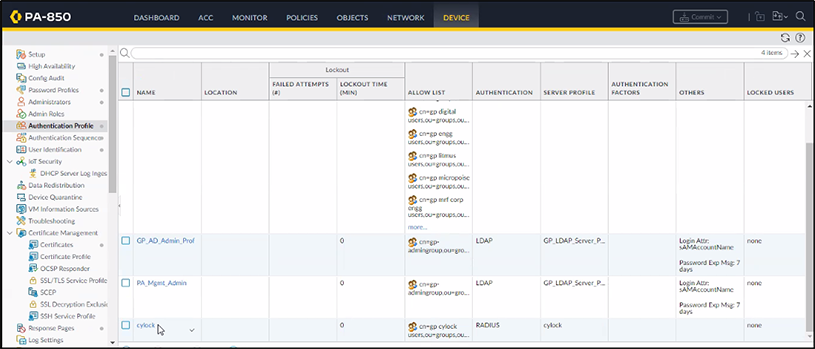
Figure 6 – Adding Authentication Profile
- Configure the Authentication Profile as shown in the below figure 5.
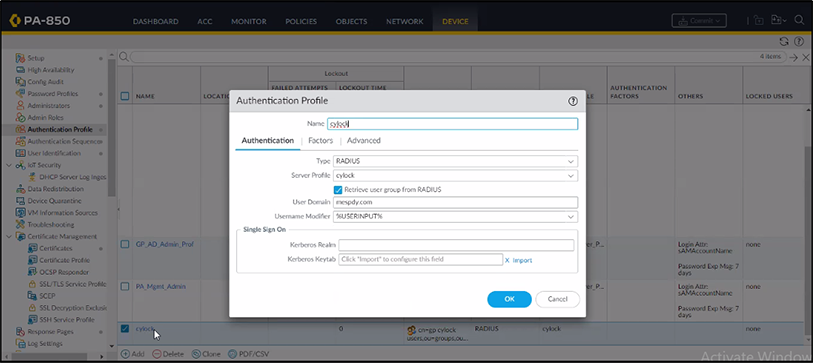
Figure 7 – Configuring Authentication Profile
- Name: Enter a friendly name for the Authentication Profile (Ex: CyLock)
- Type: RADIUS
- Server Profile:The Server profile created in the previous step 1 in Section b.
- User Domain: The domain used by your users (Optional)
- Server Accounting Port- 1646. This value is not used, but must be entered to complete the setup.
- Retry Interval- leave default at 60 seconds
- Server Secret Key- provided secret defined when setting up the app
- Common Password- leave blank.
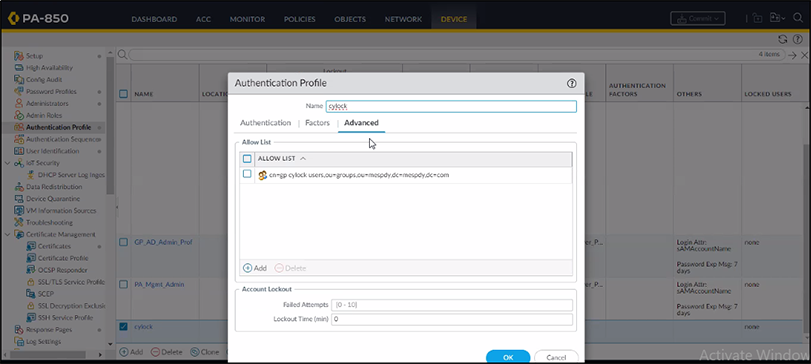
- In the same dialog, select the tab Advanced and then select “ + Add “ and add the Allow List, then click OK.
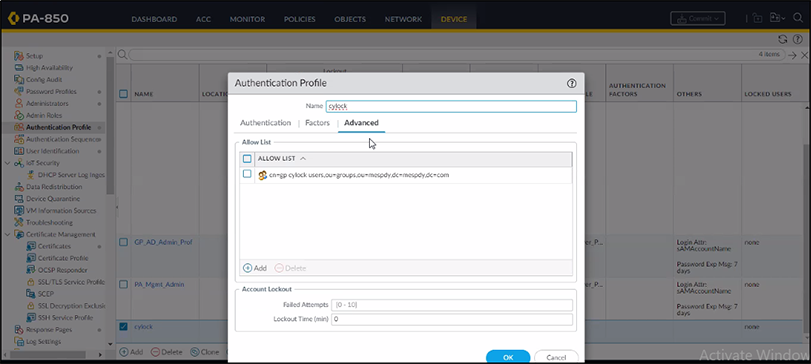
Figure 8 –Configuring Advance Settings
- Allow List: Select all or the user group(s) that you want to use for this authentication profile.
- Failed Attempts: Configure this setting according to your security policy (Optional)
- Lockout Time (min): Configure this setting according to your security policy (Optional)
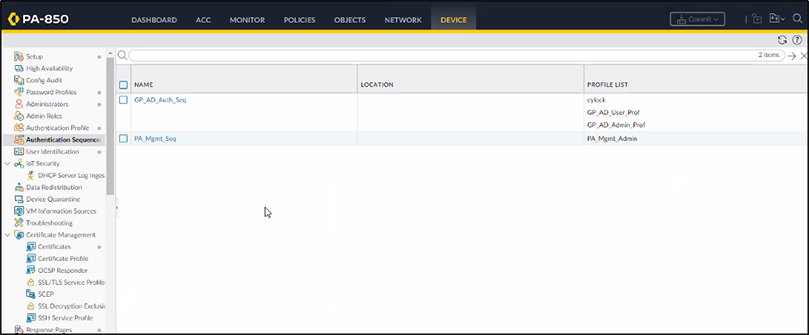
- Check that the Authentication Profile has been added to the Profile List, as shown in below Figure 7.
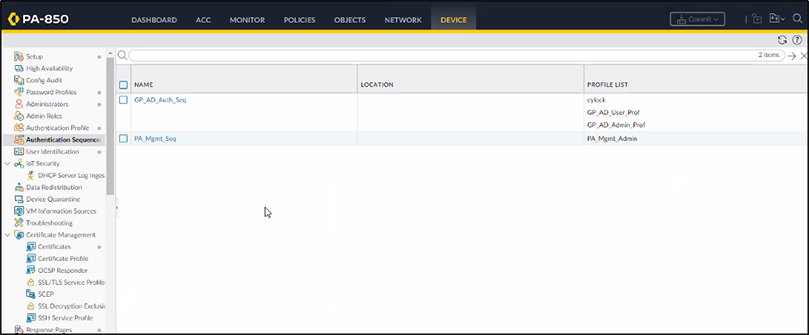
Figure 9 – Authentication Sequence Page
- Associate the RADIUS Server Profile to both Portal and gateway.
- In the Palo Alto administrative interface, select Network tab > Global Protect >
Portals.
Open the Configured Portal and add CyLock as an Agent with the respective Users/User Groups, then click OK.
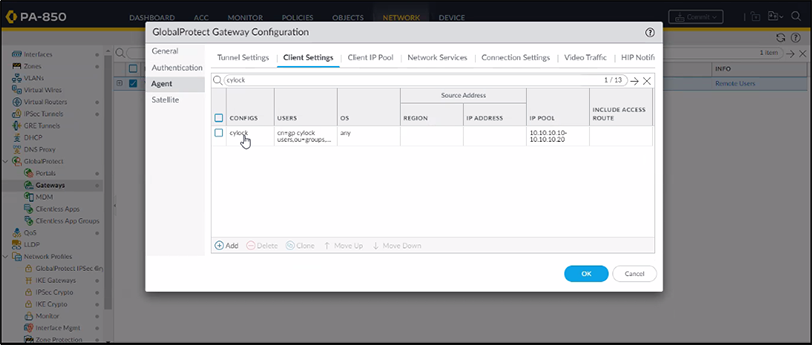
Figure 10 – Portal Configuration
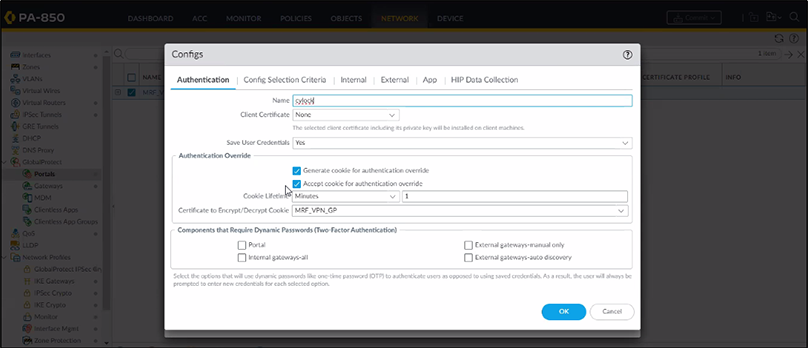
- Click Authenticationand configure the portal's authentication settings as shown below figure 9, then click Ok.
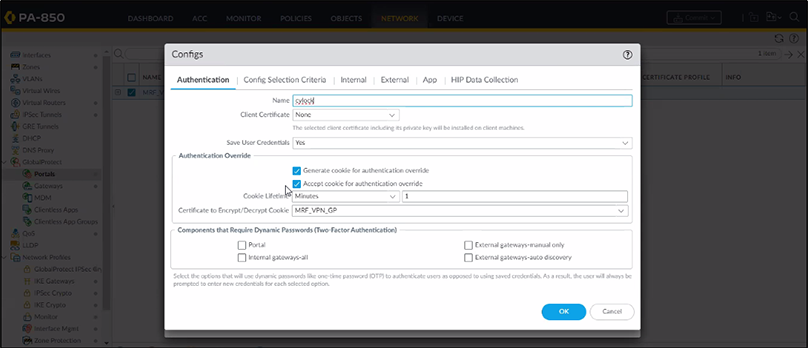
Figure 11 – Configuring Authentication Menu
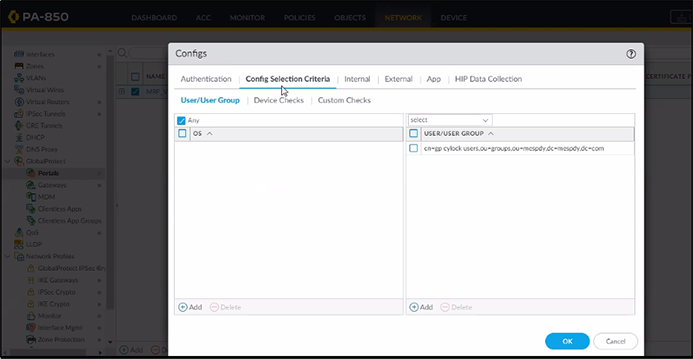
- Click Config Selection Criteriaand select the appropriate USER/USER GROUP,then click Ok.
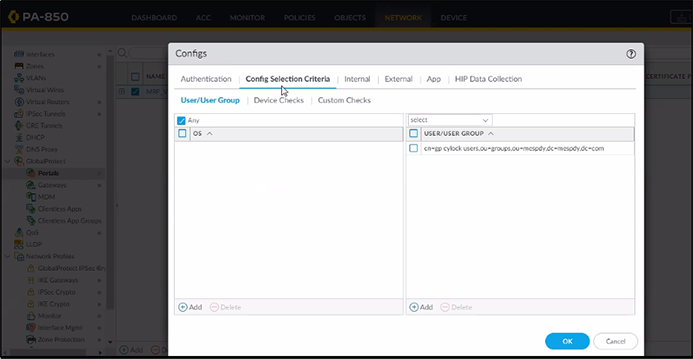
Figure 12 – Select User/User Group in Selection Criteria MenuSelect User/User Group in Selection Criteria Menu
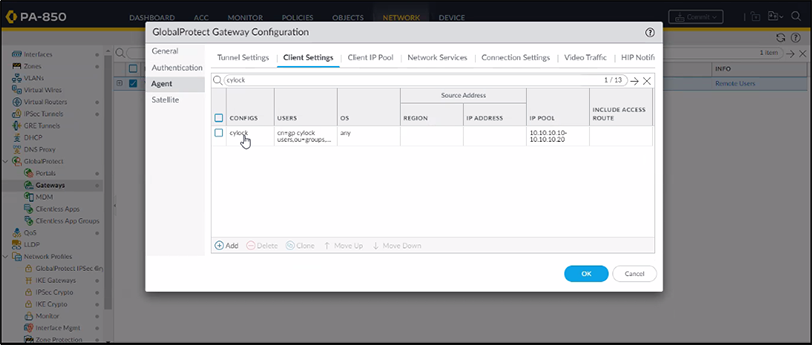
- In the Palo Alto administrative interface, selectNetwork tab > Global Protect >
Gateway.
Open the Configured gateway and edit Agent settings by double clicking the configured agent.
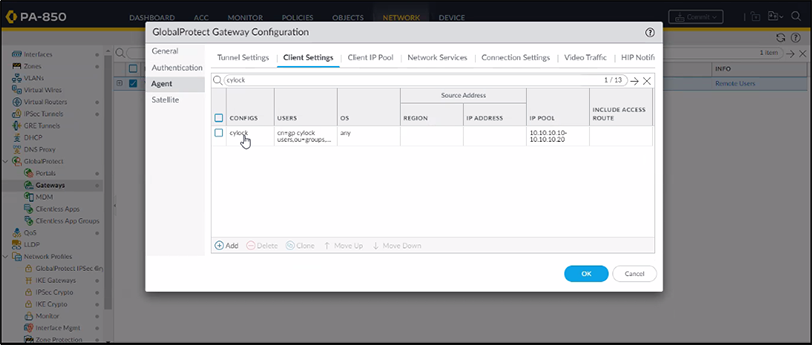
Figure 13 – Gateway Configuration
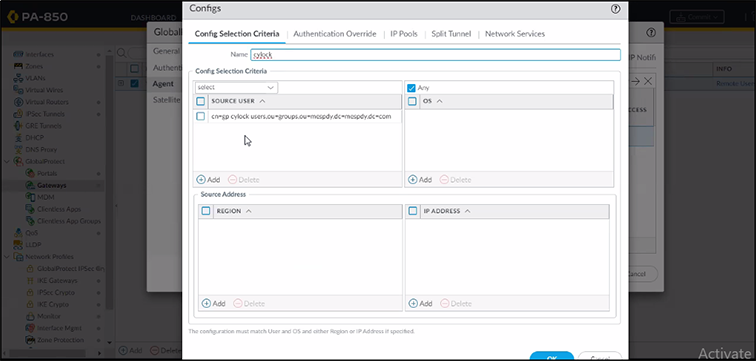
- Click Config Selection Criteriaand Select the RespectiveSOURCE USER,then click ok.
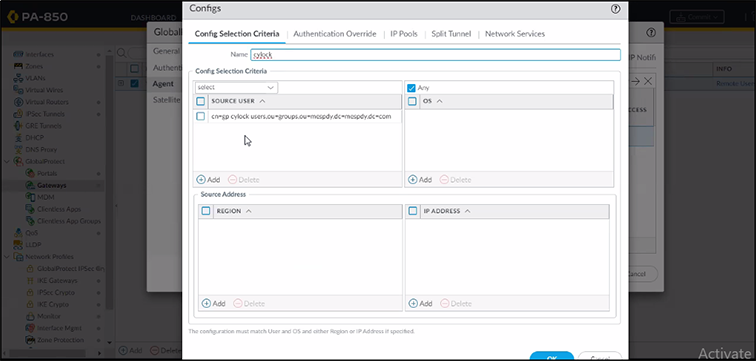
Figure 14 – Configure Selection Criteria
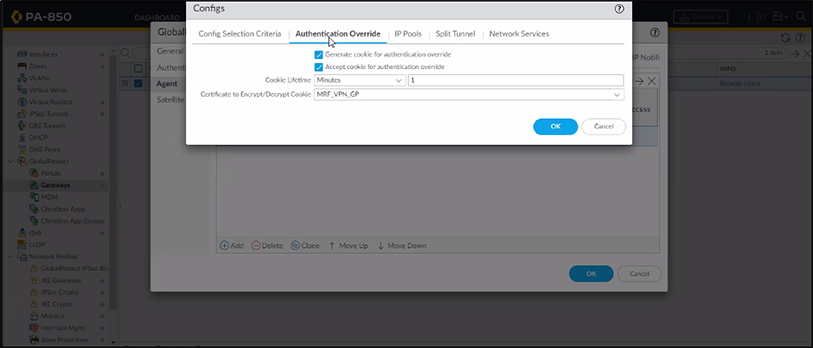
- Configure theAuthentication Overridesettings as shown in the below figure 13.
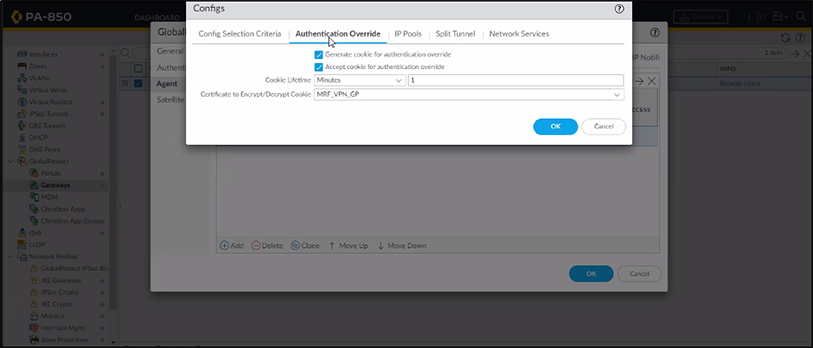
Figure 15 – Configure Authentication Override Settings
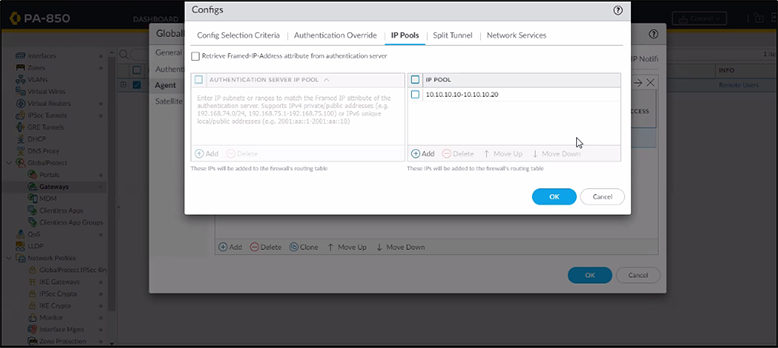
- Configure theIP Poolssettings as shown in the below figure 14.
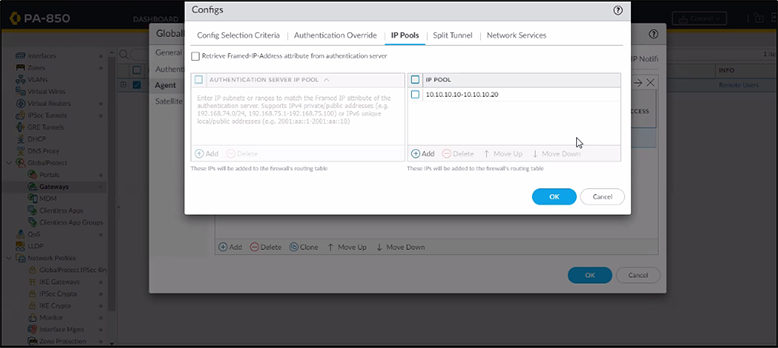
Figure 16 – Configure IP Pools
Test Your Setup
Types of Authentication Options:
CyLock allows the following Authentication during SSL VPN Login
| # |
Mode |
Process Steps |
| 1 |
Default Mode |
In password field enter << Your password >> (for carrying out the default authentication) |
| 2 |
Online (Push) |
In password field enter << Your password >>,1 (for carrying Online MFA Push authentication) |
| 3 |
Online (Push +PIN) |
In password field enter << Your password >>,2 (for carrying Online MFA Push+PIN authentication) |
| 4 |
Online (Push +Bio) |
In password field enter << Your password >>,3 (for carrying Online MFA Push+Bio authentication) |
| 5 |
Offline (CR-OTP - Display) |
In password field enter << Your password >>,4 (for carrying Offline MFA CR-OTP (Display) authentication) |
| 6 |
Offline (CR-OTP – Email) |
In password field enter << Your password >>,5 (for carrying out Offline MFA CR-OTP (Email) authentication) |
| 7 |
Offline (CR-OTP – SMS) |
In password field enter << Your password >>,6 (for carrying Offline MFA CR-OTP (SMS) authentication) |
| 8 |
Offline (POTP - Email) |
In password field enter << Your password >>,7 (for carrying out Offline MFA POTP (Email) authentication) |
| 9 |
Offline (POTP – SMS) |
In password field enter << Your password >>,8 (for carrying Offline MFA POTP (SMS) authentication) |
| 10 |
Offline (TOTP) |
In password field enter << Your password >>,9 (for carrying Offline MFA TOTP authentication) |
By using the above authentication mode, we can test VPN Connection.
Test the Connection
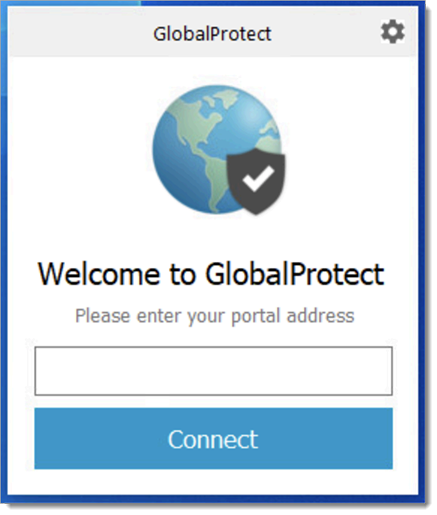
You can verify the configuration using the Global Protect VPN Client.
- Download and install the Global Protect Client. See this
link
https://docs.paloaltonetworks.com/globalprotect/4-1/globalprotect-app-user-
guide/globalprotect-app-for-windows/download-and-install-the-globalprotect-app-for-windows
for further information on how to obtain the Global Protect Client.
- Open the Global Protect Client and open Global Protect Settings.
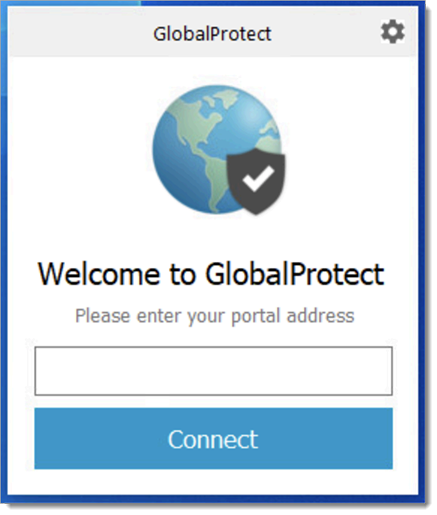
Figure 17 – Global Protect Client
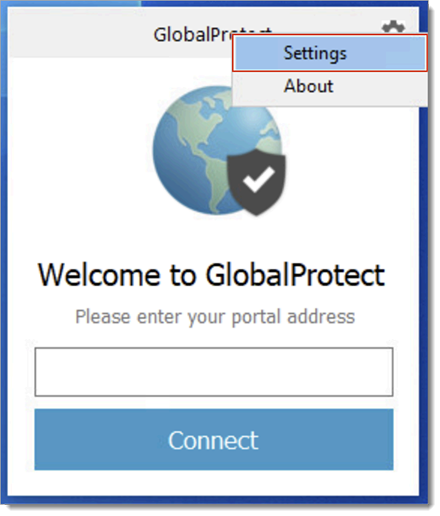
- Configure Settings as shown in the below figure 16.
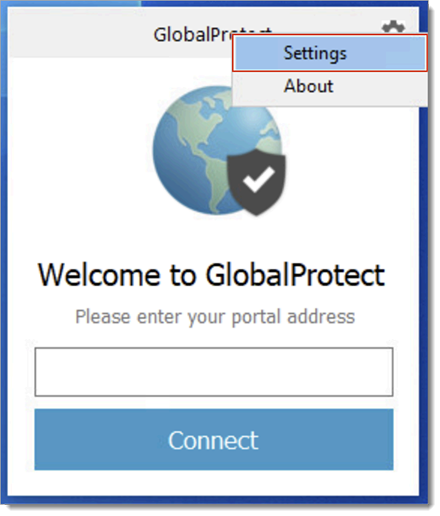
Figure 18 – Clicking Settings
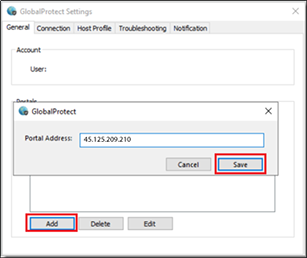
- Select Add to configure the portal created in "Configure the Palo Alto Global Protect Portal"
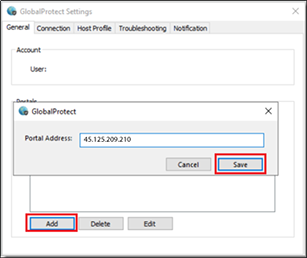
Figure 19 – Configuring General Settings
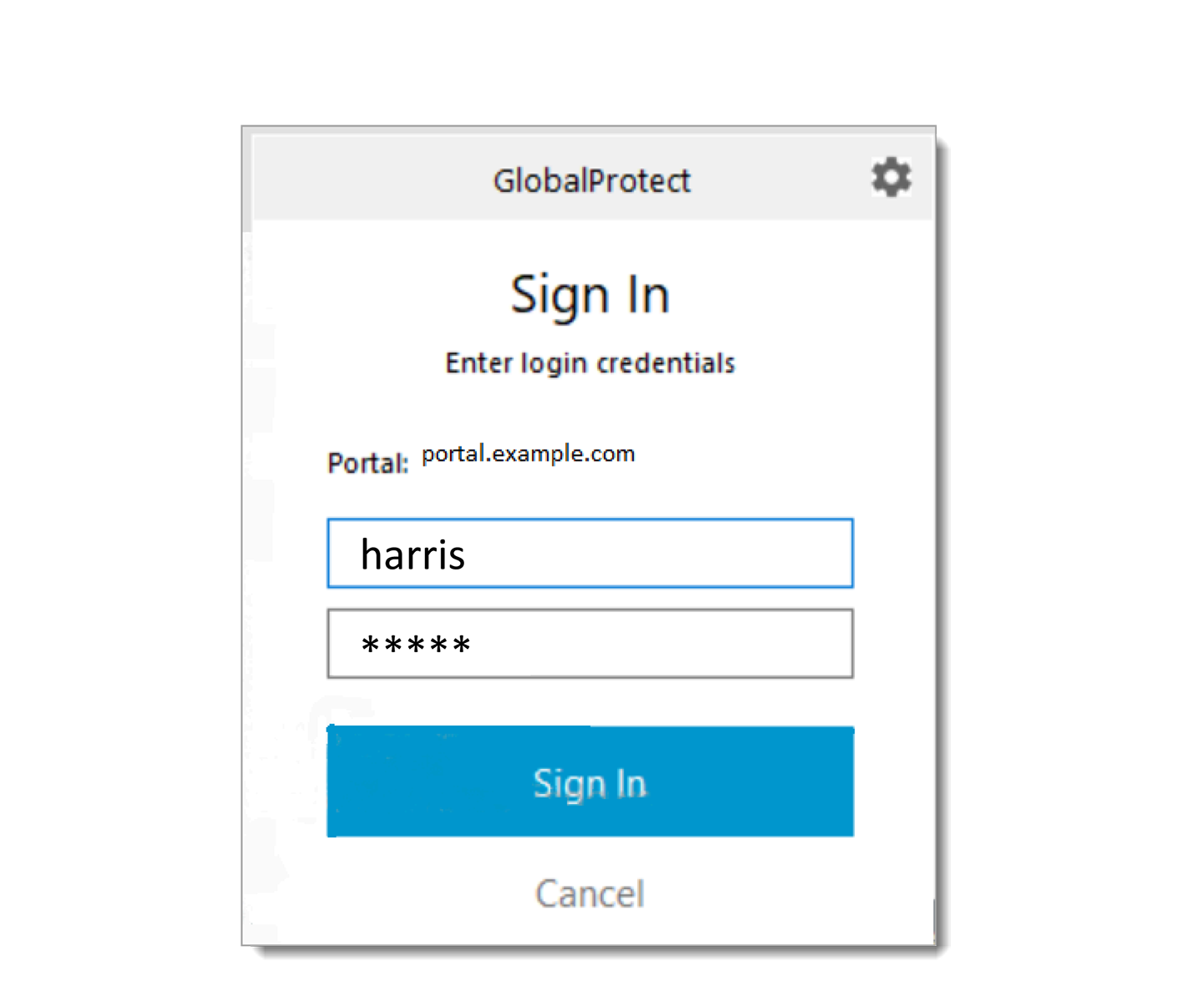
- In Global Protect client enter user name and password and click sign in.
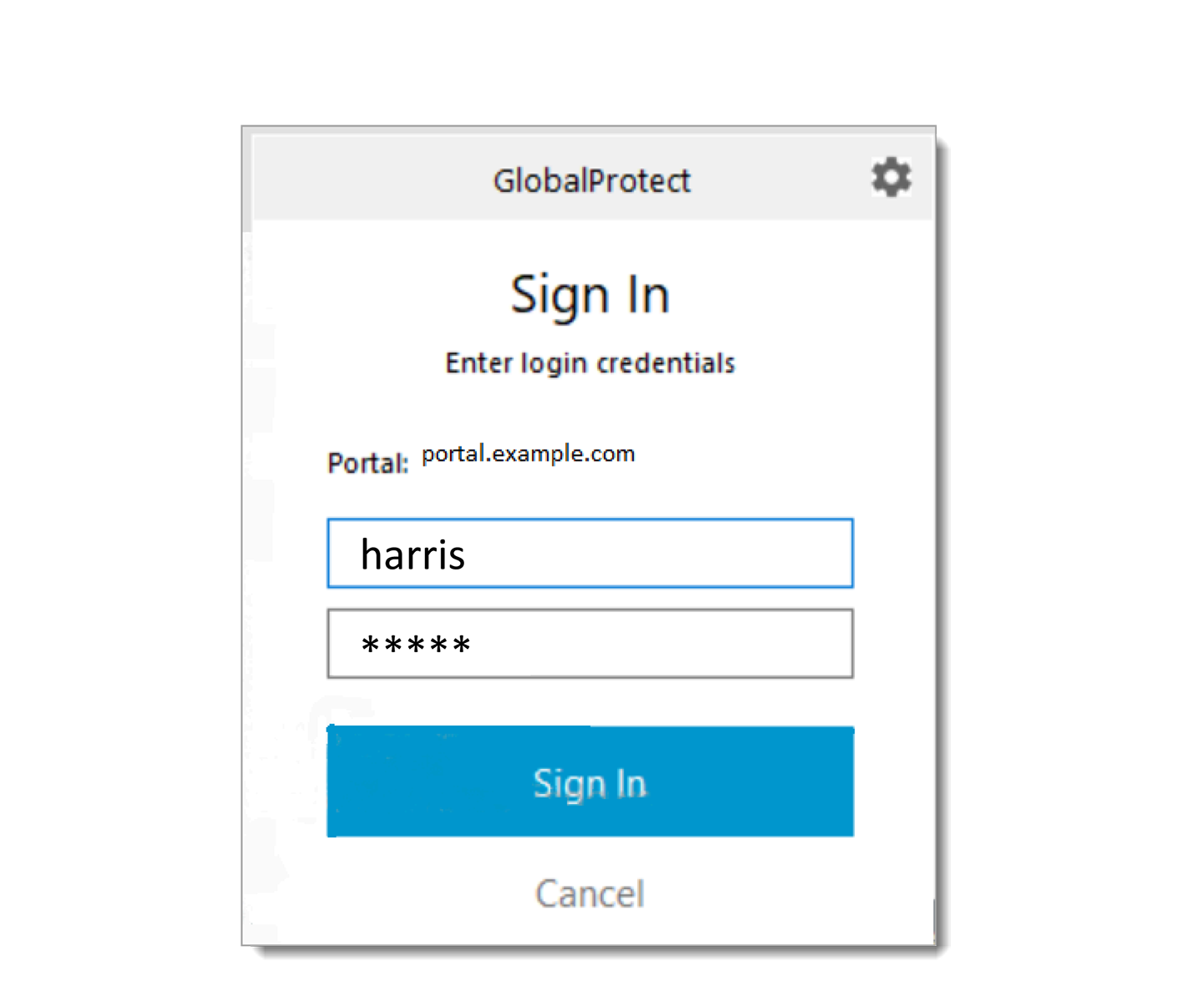
Figure 20 – Entering Login Credentials
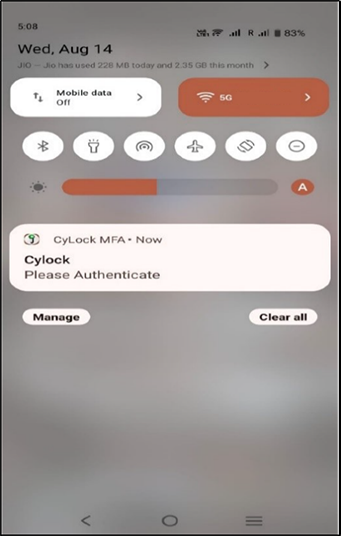
- A push notification or any preferred authentication request is sent to your mobile device as shown in the below figure 19.
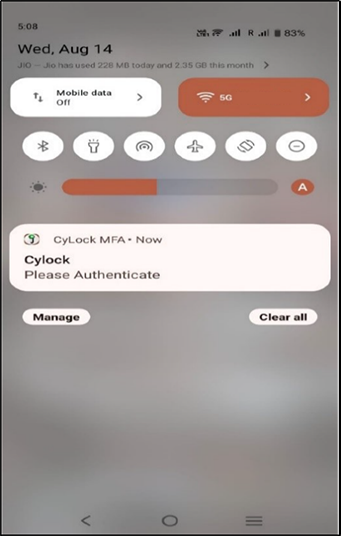
Figure 21 – Push Notification Request
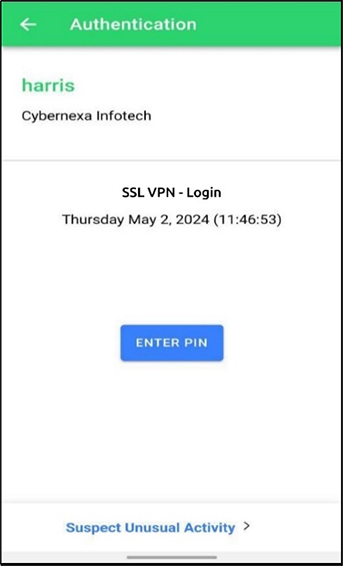
- Accept the Push + PIN request using CyLock MFA Mobile App. After the authentication is approved, the VPN connection will be established.
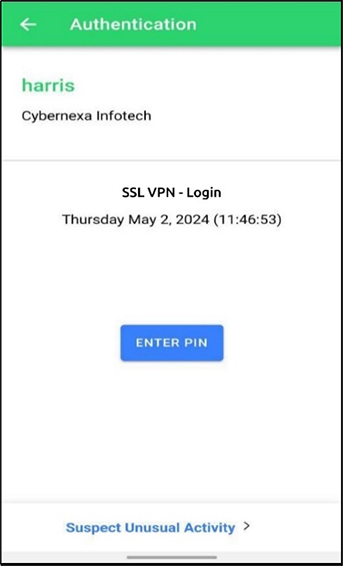
Figure 22 – Push Request
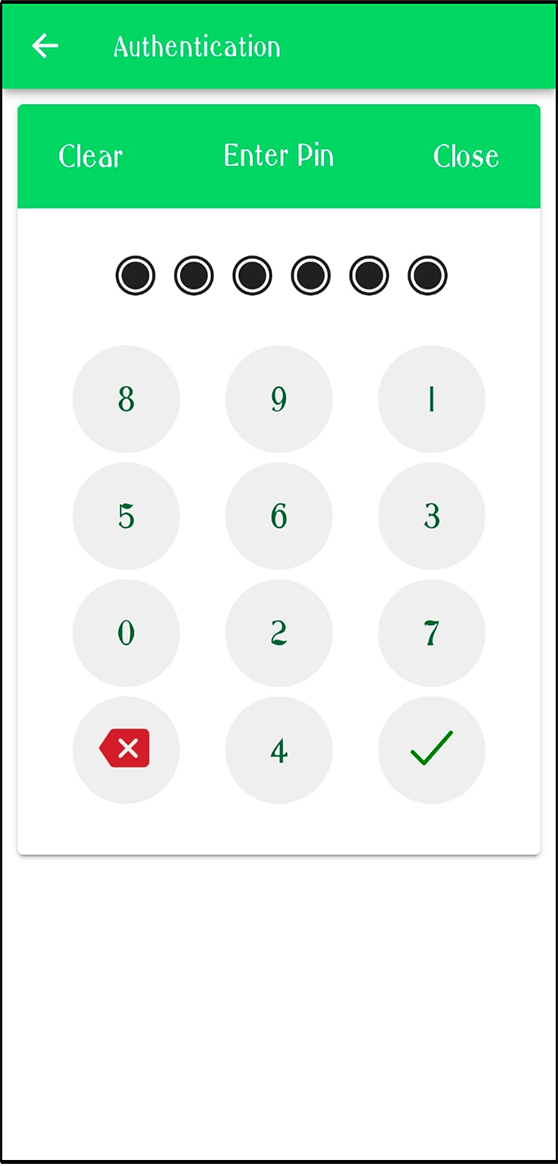
- Enter 6 Digit Pin that you have set during the device registration and then press
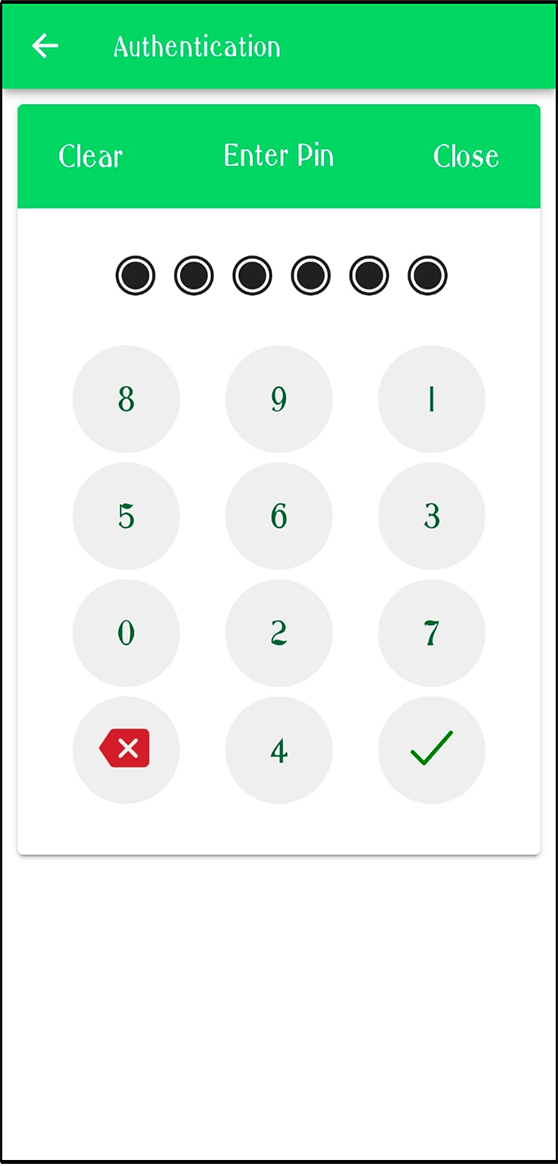
Figure 23 – Entering 6 digit PIN
- The VPN connection is established after Approval of the authentication using CyLock App will complete the VPN connection.
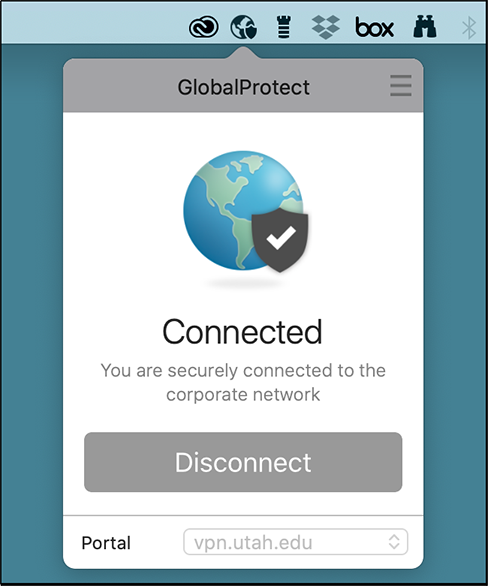
Figure 24 – SSL VPN Connection Established